It’s that time again… Microsoft Patch Day. Sometimes following Microsoft’s regular patch cycle can feel a lot like the movie, Groundhog Day. Yet—also like the movie—it’s well worth repeating regularly to make sure that you get it right.
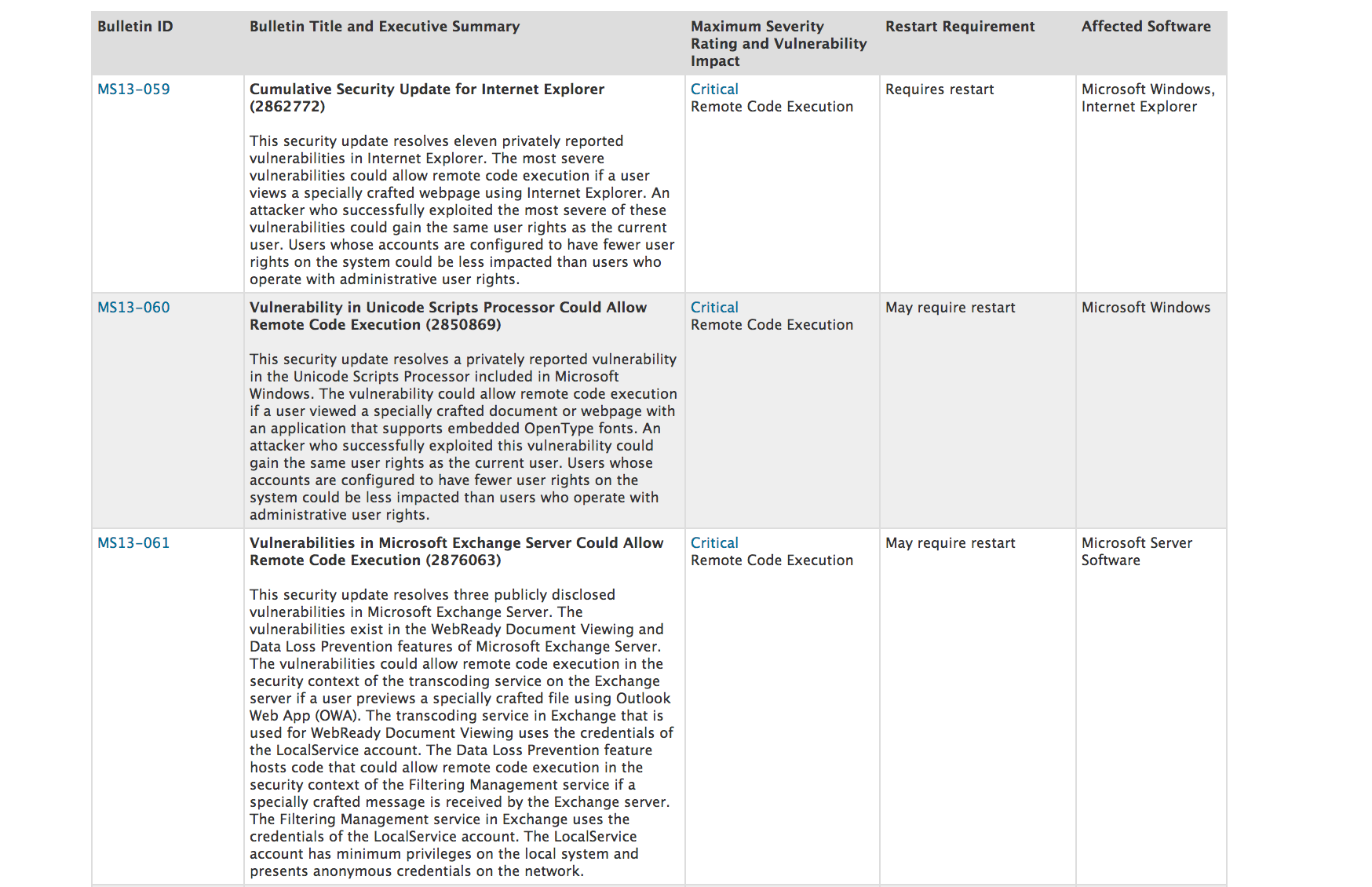
According to their summary post, Microsoft released eight security bulletins today, three of which they rate as Critical. The bulletins include updates to fix at least 22 vulnerabilities in three popular Microsoft products, Windows, Internet Explorer (IE), and Exchange Server. Though attackers aren’t exploiting these issues in the wild yet, researchers have publicly disclosed a few of them, which makes them a bit more likely to be targeted.
In my opinion, you should apply the IE update first, as it fixes 11 serious vulnerabilities, many of which attackers could leverage in drive-by download attacks. Right now, booby-trapped web sites are one of the most common infection vectors. For that reason, I recommend you apply web browser updates, like this IE one, as quickly as possible. The Exchange update is a close second, as it also fixes a remotely exploitable flaw that could allow attackers to gain access to your Exchange server simply by tricking one of your users into previewing a specially crafted document. Finish up with the Windows updates, beginning with the Critical one.
As always, I still recommend you test Microsoft patches before deploying them to your critical production servers. While it might be okay to push client software updates without testing them, you should test server updates, like today’s Exchange one, before deploying them in order to avoid unexpected downtime. If you don’t already have a test environment that mimics your production environment, virtualization is a great way to create one.
I’ll share more details about Microsoft’s bulletins in upcoming alerts, posted throughout the day. — Corey Nachreiner, CISSP (@SecAdept)

Leave a Reply