Microsoft and Adobe plan a tag team assault on computer administrators and users next Tuesday, when they intend to release a pile of Critical security updates. If you manage Windows PCs, you use at least two of the vulnerable products, and likely many more. So I recommend you gear up for a day of software updates next week.
Let’s start with Microsoft’s Patch Day.
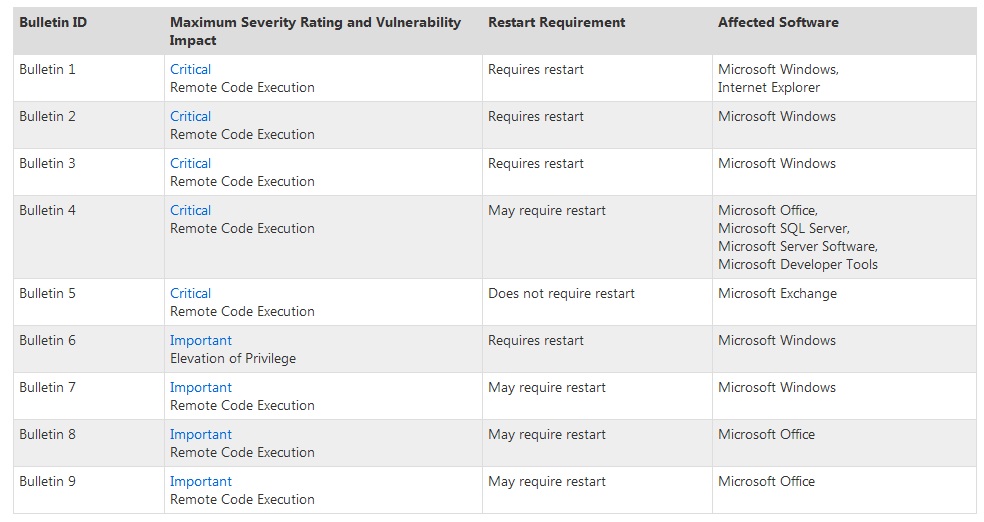 According to their August Advanced Notification, Microsoft intends to post nine security bulletins on August 14, five of which they rate as Critical. The updates fix vulnerabilities in Windows, Internet Explorer, Office, SQL Server, Exchange, and a few other products (see the image on the right for the full list).
According to their August Advanced Notification, Microsoft intends to post nine security bulletins on August 14, five of which they rate as Critical. The updates fix vulnerabilities in Windows, Internet Explorer, Office, SQL Server, Exchange, and a few other products (see the image on the right for the full list).
Microsoft hasn’t shared the details about these flaws with the public yet, but it is safe to say you should apply the Critical updates as soon as possible — especially the server related ones. Critical vulnerabilities tend to allow remote attackers to gain full control of your computer, which is bad, to say the least.
Also, during last week’s WatchGuard Security Week in Review episode I mentioned an unpatched vulnerability in Microsoft Exchange, related to its use of Oracle’s Outside In technology. I’d guess next Tuesday’s Exchange patch will probably fix this vulnerability. In short, if you manage a Windows network, prepare your team for a busy day of patching next week.
But that’s not all folks…
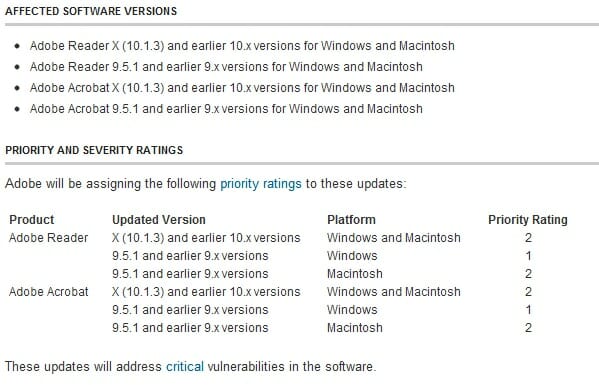 Adobe also likes to share Microsoft’s Black Tuesday, and have announced their upcoming patch day as well. Their post warns that they plan to release Adobe Reader and Acrobat X updates to fix vulnerabilities that affect both Windows and Macintosh platforms. They haven’t shared any details about the vulnerabilities in question yet, but I’m pretty sure I can accurately predict the general gist of their upcoming advisory. I’m pretty sure it will come down to, “if you open a specially crafted PDF document, attackers can leverage some flaw to execute code on your system with your privileges.”
Adobe also likes to share Microsoft’s Black Tuesday, and have announced their upcoming patch day as well. Their post warns that they plan to release Adobe Reader and Acrobat X updates to fix vulnerabilities that affect both Windows and Macintosh platforms. They haven’t shared any details about the vulnerabilities in question yet, but I’m pretty sure I can accurately predict the general gist of their upcoming advisory. I’m pretty sure it will come down to, “if you open a specially crafted PDF document, attackers can leverage some flaw to execute code on your system with your privileges.”
Since most computer users (Mac and PC users alike) install Reader, these issues will probably affect many people. Furthermore, attackers have been leveraging flaws in PDF documents in many of their spear phishing attacks lately, since many users still consider these documents as benign. If you use these popular Adobe products, plan to patch post haste.
I’ll know more about these bulletins on Tuesday, and will publish alerts about them here. — Corey Nachreiner, CISSP

Leave a Reply