Summary:
- This vulnerability affects: Adobe Flash Player running on all platforms and Adobe Air
- How an attacker exploits it: By enticing users to visit a website containing malicious Flash content
- Impact: In the worst case, an attacker can execute code on the user’s computer, potentially gaining control of it
- What to do: Download and install the latest version of Adobe Flash Player for your platform
Exposure:
Adobe Flash Player displays interactive, animated web content called Flash. Although Flash is optional, 99% of PC users download and install it to view multimedia web content. It runs on many operating systems, including mobile operating systems like Android.
 This week, Adobe released a security bulletin describing four security vulnerabilities (based on CVE numbers) that affect Flash Player running on any platform. It doesn’t describe the flaws in much technical detail, other than saying they consist mostly of buffer overflow vulnerabilities and other types of memory corruption flaws (and a cross-site scripting issue). That said, Adobe does warn that if an attacker can entice one of your users to visit a malicious website containing specially crafted Flash content, he could exploit many of these unspecified vulnerabilities to execute code on that user’s computer, with that user’s privileges. If your Windows users have local administrator privileges, an attacker could exploit this flaw to gain full control of their PCs.
This week, Adobe released a security bulletin describing four security vulnerabilities (based on CVE numbers) that affect Flash Player running on any platform. It doesn’t describe the flaws in much technical detail, other than saying they consist mostly of buffer overflow vulnerabilities and other types of memory corruption flaws (and a cross-site scripting issue). That said, Adobe does warn that if an attacker can entice one of your users to visit a malicious website containing specially crafted Flash content, he could exploit many of these unspecified vulnerabilities to execute code on that user’s computer, with that user’s privileges. If your Windows users have local administrator privileges, an attacker could exploit this flaw to gain full control of their PCs.
Though it doesn’t look like attackers are exploiting these flaws in the wild yet, Adobe rates the flaws as a “Priority 1” issues for Windows and Macintosh users, and recommends you apply the updates within 72 hours. These vulnerabilities also affect other platforms as well, such as Internet Explorer (IE) 11 and Chrome. I recommend you update any Flash capable platform as soon as you can.
Solution Path
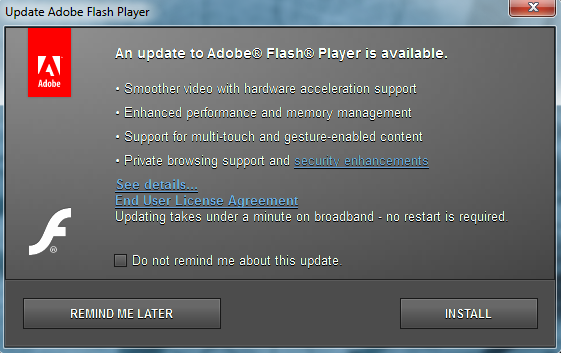
Adobe has released new versions of Flash Player to fix these issues. If you allow Adobe Flash in your network, you should download and install the new versions immediately. If you’ve enabled Flash Player’s recent “silent update” option, you will receive this update automatically.
You can download Flash for your computer at the link provided below. See the bulletin’s “Affected Software” section for more details on getting Flash updates for other platforms:
For All WatchGuard Users:
Good News! WatchGuard’s Gateway Antivirus and Intrusion Prevention services can often prevent these sorts of attacks, or the malware they try to distribute. For instance, our IPS signature team has developed signatures that can detect and block many of the memory corruption vulnerabilities described in Adobe’s alert:
- WEB Adobe Flash Player High Surrogate Parsing Cross Site Scripting (CVE-2014-0509)
- WEB-CLIENT Adobe Flash Player Information Disclosure (CVE-2014-0508)
- EXPLOIT Adobe Flash Player Memory Corruption (CVE-2014-0506)
- EXPLOIT Adobe Flash Player Memory Corruption (CVE-2014-0507)
Your XTM appliance should get this new IPS update shortly.
Furthermore, our Reputation Enabled Defense (RED) and WebBlocker services can often prevent your users from accidentally visiting malicious (or legitimate but booby-trapped) web sites that contain these sorts of attacks. Nonetheless, we still recommend you install Adobe’s Flash update to completely protect yourself from all of these flaws.
Status:
Adobe has released updates to fix these Flash vulnerabilities.
References:
This alert was researched and written by Corey Nachreiner, CISSP (@SecAdept)

How does this impact systems running Windows 8 since Flash is integrated into the OS and is not a separate install?
The frustration lies within many online marketers of the multiple
and maybe even unnecessary changes the search engines make to their so called “algorithm” and YES I will agree I have shared these frustrations.
Directories-Directories like Yellowpages, Foursquare, and Yelp can actually place you quite high on the search engine.
With online businesses, it’s very important to have good uptime,
which means no downtime.
Nice weblog right here! Additionally your web site a lot up fast!
What web host are you the usage of? Can I am getting your associate hyperlink to your host?
I wish my website loaded up as fast as yours lol
I’m really enjoying the design and layout of your blog. It’s a very easy on the eyes which makes it much more enjoyable for me to come
here and visit more often. Did you hire out a designer to create your theme?
Outstanding work!
Hello, i think that i noticed you visited my site so
i came to return the choose?.I’m trying to to find issues to improve my website!I guess its adequate to make use of some of
your ideas!!
When someone writes an post he/she retains the plan of a user in his/her mind that how a user can know it.
Thus that’s why this post is outstdanding. Thanks!
Yesterday, while I was at work, my sister stole my iphone and tested to see if
it can survive a twenty five foot drop, just so she can be a youtube sensation. My iPad is now
broken and she has 83 views. I know this is totally off topic but I had to share it with someone!
Hello, i believe that i noticed you visited my web site thus i came to go
back the prefer?.I’m trying to in finding things to improve my web site!I guess its adequate to make use of
some of your ideas!!
Wοѡ, thiѕ ρiece of writing is nice, my sister is analyzing
such things, so I am going tο inform ɦer.
This is really interesting, You are a very skilled blogger.
I have joined your rss feed and look forward
to seeking more of your magnificent post.
Also, I have shared your website in my social networks!
This excellent website certainly has all of the info I wanted concerning this subject and didn’t
know who to ask.
I was recommended this blog by my cousin. I’m not sure whether this post is written by him as nobody else know such detailed about my trouble.
You are incredible! Thanks!