Severity: High
Summary:
- These vulnerabilities affect: Adobe Flash and Shockwave Player
- How an attacker exploits them: By enticing you to run malicious Flash or Shockwave content from web pages or embedded within documents
- Impact: In the worst case, an attacker can gain complete control of your computer
- What to do: Install the appropriate Adobe patches immediately, or let Adobe’s updater do it for you.
Exposure:
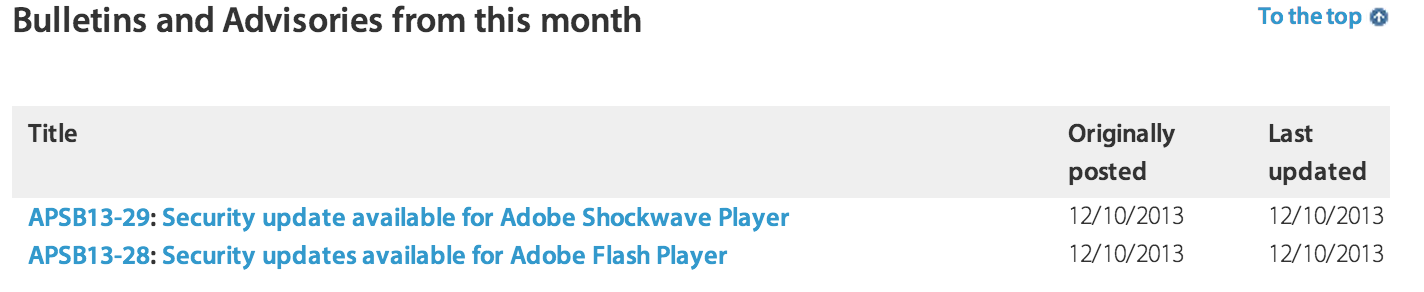
Today, Adobe released two security bulletins describing vulnerabilities in Flash and Shockwave Player. A remote attacker could exploit the worst of these flaws to gain complete control of your computer. The summary below details some of the vulnerabilities in these popular software packages.
- APSB13-29: Two Shockwave Player Memory Corruption Vulnerabilities
Adobe Shockwave Player displays interactive, animated web content and movies called Shockwave. According to Adobe, the Shockwave Player is installed on some 450 million PCs.
Adobe’s bulletin describes two unspecified memory corruption vulnerabilities that affects Shockwave Player running on Windows and Macintosh computers.They don’t share any technical details about the flaw, but do share its scope and impact. If an attacker can entice one of your users into visiting a website containing some sort of malicious Shockwave content, he could exploit the flaw to execute code on that user’s computer, with that user’s privileges. If your Windows users have local administrator privileges, an attacker could exploit this vulnerability to gain full control of their computer.
Adobe Priority Rating: 1 (Patch within 72 hours)
- APSB13-28: Zero Day Flash Player Code Execution Flaw
Adobe’s bulletin describes two vulnerabilities in Flash Player running on all platforms, including one code execution flaw attackers are currently exploiting in the wild. If an attacker can lure you to a web site, or get you to open a document containing specially crafted Flash content, he could exploit the worst of these flaws to execute code on your computer, with your privileges. If you have administrative or root privileges, the attacker could gain full control of your computer.
Adobe warns that attackers are exploiting this flaw in the wild. The attack arrives as a malicious Word document containing embedded Flash content. They have assigned these flaws their highest severity rating for Windows and Mac computers, but a lesser severity for Linux and Android devices. If you are a Windows Flash user, we recommend you apply this update immediately.
Adobe Priority Rating: 1 for Windows and Mac (Patch within 72 hours)
Solution Path:
Adobe has released updates for all their affected software. If you use any of the software below, we recommend you download and deploy the corresponding updates as soon as possible, or let Adobe’s automatic updater do it for you:
- APSB13-29: Upgrade to the latest Shockwave Player (12.0.6.147)
- APSB13-28: Upgrade to the latest Flash Player (11.9.900.170 for Windows)
Keep in mind, if you use Google Chrome you’ll have to update it separately to get the latest Flash fixes.
For All WatchGuard Users:
Attackers can exploit these flaws using diverse exploitation methods. However, WatchGuard’s XTM appliances can help in many ways. First, our IPS and AV services are often capable of detecting the malicious Flash or Shockwave files attackers are actually using in the wild. If you’d like, you can also configure our proxies to block Shockwave and Flash. This, however, blocks both legitimate and malicious content. If you do want to block this content via the Web or email, see our manual for more details on how to configure our proxy policies’ content-filtering.
Status:
Adobe has released patches correcting these issues.
References:
This alert was researched and written by Corey Nachreiner, CISSP (@SecAdept)

Leave a Reply