Severity: High
Summary:
- These vulnerabilities affect: Flash Player, Reader X, and Acrobat X. Also news of a ColdFusion zero day exploit
- How an attacker exploits them: Multiple vectors of attack, including enticing your users to open malicious files or visit specially crafted web sites
- Impact: Various results; in the worst case, an attacker can gain complete control of your computer
- What to do: Install the appropriate Adobe patches immediately, or let Adobe’s updater do it for you.
Exposure:
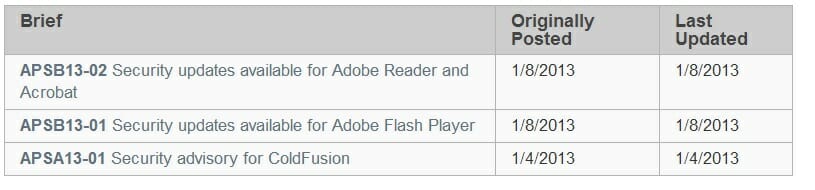
Today, Adobe released two security bulletins describing vulnerabilities in Flash Player, and Reader and Acrobat X.
A remote attacker could exploit the worst of these flaws to gain complete control of your computer. We summarize the bulletins below:
- APSB13-02: Multiple Reader and Acrobat Vulnerabilities
Adobe Reader helps you view PDF documents, while Acrobat helps you create them. Since PDF documents are very popular, most users install Reader to handle them.
Adobe’s bulletin describes 27 vulnerabilities that affect Adobe Reader and Acrobat X 11.0.0 and earlier, running on any platform (Windows, Mac, Linux). Adobe’s alert only describes the flaws in minimal detail, but most of them involve memory corruption-related vulnerabilities, such as buffer overflows, integer overflows, use-after-free issues, and so on. For the most part, they share the same scope and impact. If an attacker can entice you into opening a specially crafted PDF file, he can exploit many of these issues to execute code on your computer, with your privileges. If you have root or system administrator privileges, the attacker gains complete control of your machine.
Adobe Priority Rating: 1 for Windows (Patch within 72 hours)
- APSB13-03: Flash Player Buffer Overflow Vulnerability
Adobe Flash Player displays interactive, animated web content called Flash. Although Flash is optional, 99% of PC users download and install it to view multimedia web content. It runs on many operating systems, including mobile operating systems like Android.
Flash player suffers from a buffer overflow flaw. If an attacker can lure you to a web site, or get you to open specially crafted Flash content, he could exploit this flaw to execute code on your computer, with your privileges. If you have administrative or root privileges, the attacker could gain full control of your computer.
Adobe Priority Rating: 1 for Windows (Patch within 72 hours)
Aside from the Reader and Flash updates, Adobe also posted a warning about three zero day ColdFusion vulnerabilities that attackers are exploiting in the wild. They have not had time to fix these vulnerabilities yet, but they do offer some mitigation techniques in their advisory. If you use ColdFusion, especially as your public web server, we recommend you try to implement the mitigation techniques described in the “Mitigations” section of Adobe’s alert. We will let you know as soon as they release the real patch.
Solution Path:
Adobe has released updates for all their affected software. If you use any of the software below, we recommend you download and deploy the corresponding updates as soon as possible, or let Adobe’s automatic updater do it for you.
- APSB13-02:
- Adobe Reader X 11.0.1
- Adobe Acrobat X 11.0.1
- Adobe Reader 9.5.3 for Linux
- APSB13-03:
- Download the latest Flash Player
- Android and Chrome users must update via Google.
For All WatchGuard Users:
Attackers can exploit these flaws using diverse exploitation methods. Though our IPS and AV services may help prevent some of these attacks, or the malware they try to load, installing Adobe’s updates is your most secure course of action.
Status:
Adobe has released patches correcting these issues.
References:
This alert was researched and written by Corey Nachreiner, CISSP (@SecAdept).

I see a lot of interesting articles on your page. You have to spend a lot of time writing, i know how
to save you a lot of work, there is a tool that creates unique, SEO friendly posts in couple of
minutes, just type in google – laranita’s free content
source
I read a lot of interesting content here. Probably you spend a lot of time writing, i know how to save you a lot of work, there is an online tool that creates
unique, google friendly articles in seconds, just type in google – laranitas free content
source