Summary:
- This vulnerability affects: Adobe Flash Player 11.1.102.62 and earlier, running on all platforms (including Android)
- How an attacker exploits it: By enticing users to visit a website containing malicious Flash content
- Impact: In the worst case, an attacker can execute code on the user’s computer, potentially gaining control of it
- What to do: Download and install the latest version of Adobe Flash Player (version 11.1.102.63 for computers)
Exposure:
Adobe Flash Player displays interactive, animated web content called Flash. Although Flash is optional, 99% of PC users download and install it to view multimedia web content. It runs on many operating systems, including some mobiles like Android.
 In an unexpected security bulletin released today, Adobe warned of an update that fixes two security vulnerabilities in Adobe Flash Player 11.1.102.62 and earlier, running on all platforms (including Android). Adobe’s bulletin doesn’t describe the flaws in much detail (one is a “memory corruption” and the other is an “integer error”) but it does warn that if an attacker can entice one of your users to visit a malicious website containing specially crafted Flash content, he could exploit the worst of these vulnerabilities to execute code on that user’s computer, with that user’s privileges. If your Windows users have local administrator privileges, an attacker could exploit this flaw to gain full control of their PCs.
In an unexpected security bulletin released today, Adobe warned of an update that fixes two security vulnerabilities in Adobe Flash Player 11.1.102.62 and earlier, running on all platforms (including Android). Adobe’s bulletin doesn’t describe the flaws in much detail (one is a “memory corruption” and the other is an “integer error”) but it does warn that if an attacker can entice one of your users to visit a malicious website containing specially crafted Flash content, he could exploit the worst of these vulnerabilities to execute code on that user’s computer, with that user’s privileges. If your Windows users have local administrator privileges, an attacker could exploit this flaw to gain full control of their PCs.
Adobe calls this a “Priority 2” update, which means it fixes fairly critical flaws, but that attackers are not exploiting the flaws in the wild yet. Adobe suggests you patch these flaws within 30 days. I recommend that you try to do it within the week.
Solution Path
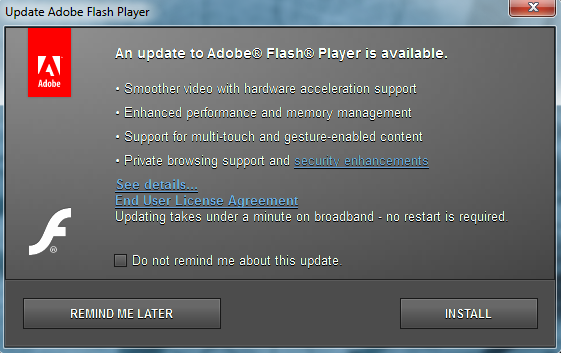
Adobe has released new versions of Flash Player (11.1.102.63 for computers and 11.1.11x.x for Android) to fix these issues. If you allow Adobe Flash in your network, you should download and install the new versions immediately:
- Download Flash Player for your computer [any platform]:
- Download Flash for Android 4.x [Visit from your Android device]
- Download Flash Player for Android 3.x and below [Visit from your Android device]
For All WatchGuard Users:
If you choose, you can configure the HTTP proxy on your XTM appliance to block Flash content. Keep in mind, doing so blocks all Flash content, whether legitimate or malicious.
Our proxies offer many ways for you to block files and content, including by file extension, MIME type, or by using very specific hexidecimal patterns found in the body of a message – a technique sometimes referred to as Magic Byte detection. Below I list the various ways you can identify various Flash files:
File Extension:
- .flv – Adobe Flash file (file typically used on websites)
- .fla – Flash movie file
- .f4v – Flash video file
- .f4p – Protected Flash video file
- .f4a – Flash audio file
- .f4b – Flash audiobook file
MIME types:
- video/x-flv
- video/mp4 (used for more than just Flash)
- audio/mp4 (used for more than just Flash)
FILExt.com reported Magic Byte Pattern:
- Hex FLV: 46 4C 56 01
- ASCII FLV: FLV
- Hex FLA: D0 CF 11 E0 A1 B1 1A E1 00
(Keep in mind, not all the Hex and ASCII patterns shared here are appropriate for content blocking. If the pattern is too short, or not unique enough, blocking with them could result in many false positives)
If you decide you want to block Flash files, the links below contain instructions that will help you configure your Firebox proxy’s content blocking features using the file and MIME information listed above.
- XTM Appliance with WSM 11.x
- Firebox X Edge running 10.x
- Firebox X Core and X Peak running Fireware 10.x
Status:
Adobe has released updates to fix these Flash vulnerabilities.
References:
This alert was researched and written by Corey Nachreiner, CISSP (@SecAdept)

Leave a Reply